Lab: SQL injection attack, querying the database type and version on MySQL and Microsoft | Web Security Academy
![Database schema for the port scanning portion of the vulnerability scanner - Hands-On Penetration Testing with Python [Book] Database schema for the port scanning portion of the vulnerability scanner - Hands-On Penetration Testing with Python [Book]](https://www.oreilly.com/library/view/hands-on-penetration-testing/9781788990820/assets/141d4225-3855-413c-8695-4035266bdcad.png)
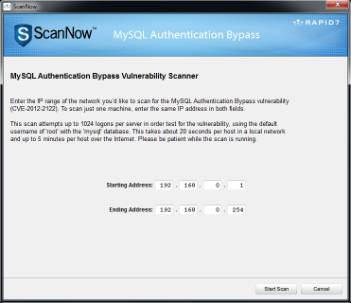
Database schema for the port scanning portion of the vulnerability scanner - Hands-On Penetration Testing with Python [Book]

How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog